





Published on Jan 09, 2026
With the support of ATM, though banking becomes easier but the chances of fraud are on rampant. There has been countless number of mishap and misrepresentations which usually occurs of in banking transactions. Thus, there is a dire need for development of such system which would serve to protect the consumers from fraud and other breaches of security. This paper proposes the alliance of Face Recognition System for verification process and enhancing the security in the banking region
The rise of technology into India has brought into force many type of equipment that aim at more customer satisfaction.ATM is one such machine which made money transaction easy for customers to the bank. But it has both advantages and disadvantages. Current ATMs make use of naught more than an access card and PIN for uniqueness confirmation. [1]This has ATM Using Face Recognition System demonstrate the way to a lot of fake attempt and mistreatment through card theft, PIN theft, stealing and hacking of customers account details and other parts of security. This process would effectively become details and other part of security. This process would effectively become an exercise in pattern matching, which would not require a great deal of time.
FRS is an application that mechanically identifies a person from a digital image or a video outline from a video source. [2] One of the behaviors to do this method is by matching chosen facial features from a facial database and the image. In this system, with appropriate lightning and robust learning. Further a positive visual match would cause the live image to be stored in the database so that future transactions would have broader base from which to compare if the original account image fails to provide a match –thereby decreasing false negatives.

A database of peoples face is maintained by the system that handles face detection. There are typically 3 parts related to a face recognition:
Face-detector,
Eye-localizer
Face-recognizer
The face detector spot the face, eliminating any other detail, not related to the face (like the backdrop). It identifies the facial region and leaves the non-facial region in the photo of the person to be identified.
It finds the spot of the eyes; so that the position of the face can be identify better
It will check the database to find a match.
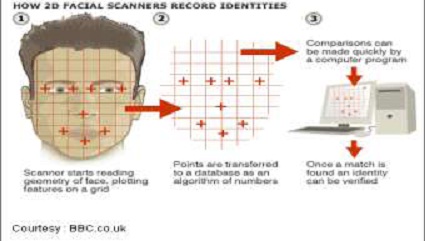
The first and foremost important step of this system will be to locate a powerful open source facial recognition program that uses local feature analysis and that is targeted at facial verification. Various facial recognition algorithms be familiar with faces by extracting features, from a snap of the subject's face. For ex, an algorithm may examine the size, relative position, in addition to/or outline of the nose, eyes, cheekbone and jaw. These facial appearances are then used to search for other imagery across matching features. Other algorithm manages a balcony of face images and then compresses the images face information and it saves only the data in the image that is used for face detection.
They are of three types:
2-D
3-D
Surface Texture Analysis.
The 2-D recognition method was individual of the original techniques employed. It maintained details of people‟s faces as seen two dimensionally. [3] Details like width of the nose, width of the eyes, distance between the eyes, jaw line, cheek bone figure were used for contrast. This type of face recognition was not too precise. Change in facial expression or difference in ambient lighting on an appearance that is not directly looking into the camera did not produce expected results.
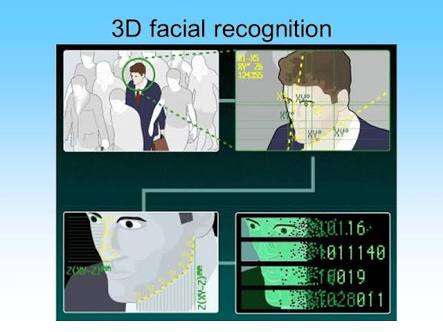
Progression in face recognition gave origin to the 3-D recognition system. This stepped up technique, used facial appearance like contours of the eye sockets, chin, nose, peaks and valley on the visage for identification. The database will store details of faces also. The advantage of 3- D technique over 2-D method is that 3-D face identification works fine even if the face is turned at 90 degree to the camera. It is self-governing of lighting environment and facial expressions.
The most superior method is Surface Texture Analysis (STA). STA does not examine the entire face but a patch of membrane on it. This patch is divided into separate blocks. The skin surface, the pore on the skin and other face characteristics are converted to a code. This code is used for comparison
In spite of all these security features; a new technology has been developed. Bank United of Texas became the first in the United States to offer iris recognition technology at automatic teller machines, providing the customers a card less, password-free way to get their money out of an ATM. [4] there‟s no card to show, there's no fingers to ink, no customer inconvenience or discomfort. It's just a photograph of a Bank United customer's eyes. Iris recognition is an automated method of biometric identification that uses mathematical pattern-recognition techniques on video images of one or both the issues of an individual‟s eyes whose complex patterns are unique, stable, and can be seen from some distance. A key advantage of Iris recognition besides its speed of matching and its extreme resistance to false matches, is the stability of the Iris as an internal and protected, yet externally visible organ of an eye. Figure below shows an schematic diagram of Iris recognition.

Just step up to the camera while your eye is scanned. The iris -- the colored part of the eye the camera will be checking -- is unique to every person, more so than fingerprints. [4] And, for the customers who can't remember their personal identification number or password and scratch it on the back of their cards or somewhere that a potential thief can find, no more fear of having an account cleaned out if the card is lost or stolen.
When a customer puts in a bankcard, a stereo camera locates the face, find the eye and take a digital image of iris at a distance of up to two to three feet. The result computerized „iris code‟s compared with one of the customer will initially provide the bank. ATM won‟t work if the two codes don‟t match. The camera also does not use any kind of beam. Instead, a special lens has been developed that will not only blow up the image of the iris, but provide more detail when it does. Iris scans are more accurate than other high-tech id system available that scan voices and fingerprints.
We thus develop an ATM model which provides security by using Facial verification software Adding up facial recognition systems to the identity confirmation process used in ATMs can reduce forced transactions to a great extent. Using a 2d and 3d technology for identification is strong and it is further fortified when another is used at auntheticiation level.
[1] Faune Hughes Daniel Lighter Richard Oswald Michael Whitfield "Face Biometrics: A Longitudinal Study" <em>Seidenberg School of CSIS Pace University</em>.
[2] Gary G. Yen Nethrie Nithianandan "Facial Feature Extraction Using Genetic Algorithm Intelligent Systems and Control Laboratory School of Electrical and Computer Engineering‟‟
[3] Bone, Mike, Wayman, Dr. James L., and Blackburn, Duane.“Evaluating Facial Recognition Technology for Drug Control Applications.” ONDCP International Counterdrug Technology Symposium: Facial Recognition Vendor Test., June 2001.
[4] S. Sruthy. "Literature Survey Automated Person Identification Techniques." (2013)
| Are you interested in this topic.Then visit the below page to get the full report |