





Updated on Mar 21, 2026
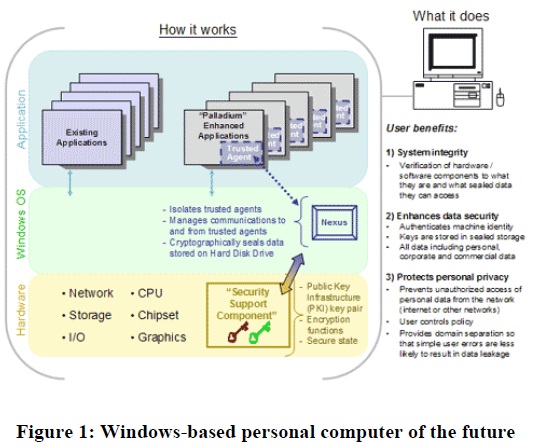
"Palladium" is the code name for an evolutionary set of features for the Microsoft® Windows® operating system. When combined with a new breed of hardware and applications, these features will give individuals and groups of users greater data security, personal privacy, and system integrity. In addition, "Palladium" will offer enterprise customers significant new benefits for network security and content protection.
Users implicitly trust their computers with more of their valuable data every day. They also trust their computers to perform more and more important financial, legal and other transactions. "Palladium" provides a solid basis for this trust: a foundation on which privacy- and security-sensitive software can be built.
There are many reasons why "Palladium" will be of advantage to users. Among these are enhanced, practical user control; the emergence of new server/service models; and potentially new peer-to-peer or fully peer-distributed service models. The fundamental benefits of "Palladium" fall into three chief categories: greater system integrity, superior personal privacy and enhanced data security.
Development of "Palladium" is guided by important business and technical imperatives and assumptions. Among these are the following: A "Palladium"-enhanced computer must continue to run any existing applications and device drivers. "Palladium" is not a separate operating system. It is based on architectural enhancements to the Windows kernel and to computer hardware, including the CPU, peripherals and chipsets, to create a new trusted execution subsystem=
"Palladium" will not eliminate any features of Windows that users have come to rely on; everything that runs today will continue to run with "Palladium." In addition, "Palladium" does not change what can be programmed or run on the computing platform; it simply changes what can be believed about programs, and the durability of those beliefs. Moreover, "Palladium" will operate with any program the user specifies while maintaining security. "Palladium"-based systems must provide the means to protect user privacy better than any operating system does today. "Palladium" prevents identity theft and unauthorized access to personal data on the user's device while on the Internet and on other networks. Transactions and processes are verifiable and reliable (through the attestable hardware and software architecture described below), and they cannot be imitated.
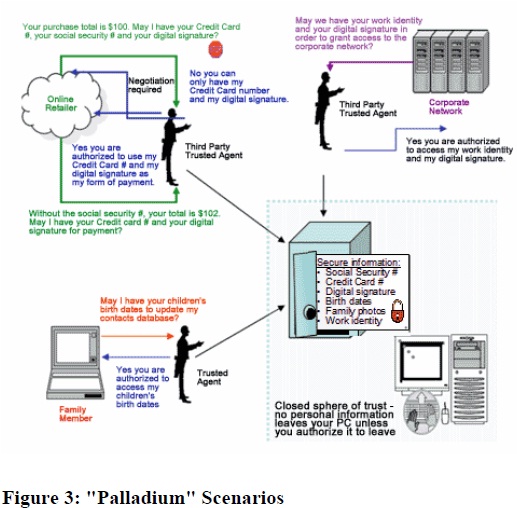
With "Palladium," a system's secrets are locked in the computer and are only revealed on terms that the user has specified. In addition, the trusted user interface prevents snooping and impersonation. The user controls what is revealed and can separate categories of data on a single computer into distinct realms.
"Palladium" is entirely an opt-in solution; systems will ship with the "Palladium" hardware and software features turned off. The user of the system can choose to simply stay with this default setting, leaving all "Palladium"-related capabilities (hardware and software) disabled.
Palladium must be highly resistant to software attacks (such as Trojan horse viruses), and must provide users with the integrity of a protected, end-to-end system across networks. Palladium provides a trusted processing environment. Trusted code runs in memory that is physically isolated, protected, and inaccessible to the rest of the system, making it inherently impervious to viruses, spy-ware, or other software attacks. With respect to viruses, the contribution from Palladium is fairly straightforward. Since Palladium does not interfere with the operation of any program running in the regular Windows environment, everything, including the native OS and viruses, runs there as it does today. So antivirus monitoring and detection software in Windows will still be needed.
However, Palladium does provide antivirus software with a secure execution environment that cannot be corrupted by infected code, so an antivirus program built on top of a Palladium application could guarantee that it hasn't been corrupted. This grounding of the antivirus software allows it to bootstrap itself into a guaranteed execution state, something it can't do today.
One of the key Palladium building blocks is "authenticated operation". If a banking application is to be trusted to perform an action, it is important that the banking application has not been subverted. It is also important that banking data can only be accessed by applications that have been identified as trusted to read that data. "Palladium" systems provide this capability through a mechanism called sealed storage. Another capability provided by authenticated operation is attestation. "Palladium" will allow a bank to accept only transactions initiated by the user and that are not viruses or other unknown machines on the Internet.
Because "Palladium" software and hardware is cryptographically verifiable to the user and to other computers, programs and services, the system can verify that other computers and processes are trustworthy before engaging them or sharing information. Users therefore can be confident that their intentions are properly represented and carried out, as illustrated in Figure 3. Moreover, the source code for the operating system's critical nexus will be published and validated by third parties. Finally, interaction with the computer itself is trusted. "Palladium"-specific hardware provides a protected pathway from keyboard to monitor, and keystrokes cannot be snooped or spoofed, even by malicious device drivers.
White paper on “Microsoft Palladium” by Electronic Privacy Information Centre.
Details about Palladium on the web site Microsoft.com.
| Are you interested in this topic.Then mail to us immediately to get the full report.
email :- contactv2@gmail.com |