



Published on Nov 30, 2023
Motion Detection and Instant Alerter Project is to develop a system to detect physical intrusion using a web cam and to alert the user of the same by making a call to the user’s mobile, using a dialup modem connected to the computer.
Detecting regions of change in multiple images of the same scene taken at different times is of widespread interest due to a large number of applications in diverse disciplines, including remote sensing, surveillance, medical diagnosis and treatment, civil infrastructure, and underwater sensing. To implement the above process for the comparison of the two images, we adopt one of the image change detection algorithms called Simple Differencing Algorithm.
“Simple Differencing Algorithm“, the rule which is used to compute the difference between two images says D(x)=I2(x)-I1(x). In this algorithm, the motion cannot be detected. This concept of Simple Differencing Algorithm is extended to detect the motion by capturing multiple images at regular intervals of the same scene. This motion detection technique is adopted to use in Motion Detection and Instant Alerter.
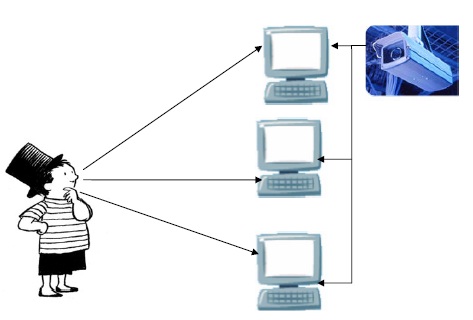
The project aims to develop a system to detect physical intrusion using a web cam and to alert the user of the same by making a call to the user’s mobile, using a dialup modem connected to the computer. The system captures the image of the intruder at the same time and saves it to the database which can be viewed at a later time to identify the intruder. The intrusion can be intimated to the server and the image which is taken at the time of intrusion is also sent to the server connected through a LAN or Internet.
The objective of this project is to maintain security in restricted areas such as bank lockers, jewelry shops etc. Security is maintained by taking constant Snapshots for every 100 microseconds using a web camera. Every Snapshot is compared with the next Snapshot to monitor changes. Also as soon as Intrusion is detected the user (security) is alerted immediately by making a call to his phone through a dial-up modem. The intrusion is also intimated to the Server which is connected through a LAN or internet. The system also takes snapshots of the intrusion and saves it in the client. These images are stored according to the date and time in which the Intrusion was detected for easy viewing. Also an alarm is raised at both the client and the server side. Moreover the photo that was taken during Intrusion detection is sent to the Server. Thus effectively detecting Intrusion and alerting immediately. C# and .net is used to develop the system.
To avoid the insufficiency in the previous systems new system with the following features is proposed .
1. In this system it only starts saving the images only when the motion is detected
2. The pictures are compared by the DIFFERENCE AND THRESHOLD ALGORITHM.
3. Two threshold values are fixed
• Threshold1: Helps to compare two pictures.
• Threshold2: Helps to compare two pixels.
• Each and every pixel is compared, both height and width.
• If the comparison value exceeds the threshold2 value, the two compared pixels are different.
• If the comparison value exceeds the threshold1 value .Then the user/server is alerted.
4.The system alerts the user by three ways, • Alerting the user’s mobile.
• Informs the server, saving images to database and sends it to the server where server may be in any location.
• Raising the alarm in the physical location.
5.The whole system can be controlled by the server from any location.
Our project has been organized in the following pattern. During the beginning of the project, first step was to accumulate the background knowledge about Motion Detection concepts. This served as the necessary ground work for us to work on the application. Subsequently we ventured into the various existing motion detection techniques which provided us with various ideas on which we could improvise, in this phase we studied the motion detection algorithm. Our next step was to analyze the software requirement, cost estimation and project schedule. Further this project was divided into five modules .The code programming was done in C# and .Net. Enclosed is the implementation of various modules. Finally we have provided references from where we collected information about the various aspects of the project. This references will be useful for any further improvisations of the project.
PROCESSOR : Pentium/Athelon processor.
RAM : 256 MB.
Operating system : Windows xp.
Other : Camera.(WEB CAMERA),
Dialup modem connected to a phone line,
System connected through a LAN
Microsoft .NET Technology
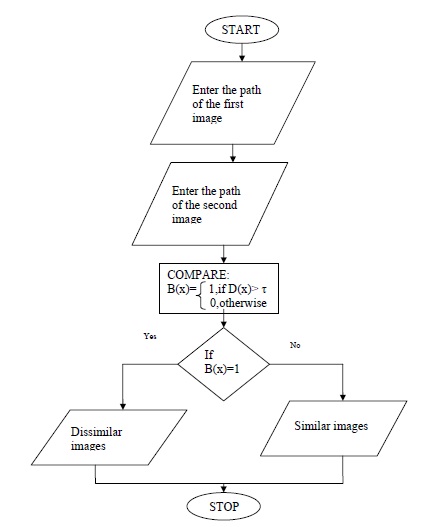
The image is taken for every 100 microseconds. Every image taken is compared to the next image with the help of Difference and Threshold Algorithm .In this technique every image is traversed through height and width, so that each and every pixel is compared. There are two threshold values. Threshold 1 is used to compare two pictures i.e. used to compare two pictures are similar.
Threshold 2 is used to compare two pixel points. Here each and every pixel points are compared in the two images. While comparing two pixels, if the comparison value exceeds threshold2 value then the two pixels are different. After comparing all the pixel points, the total numbers of differences in the pixel points are compared to the Threshold1 value. If the comparison value exceeds Threshold1 value then the two images are different. Thus Intrusion is detected effectively.
Our project on Motion Detection and Instant Alerter will effectively be used for preventing unauthorized persons from entering restricted area by monitoring them using a web camera. The sensitivity of the system can also be adjusted such that even a slight change will result in an alarm. Thus it provides more security for banking sectors. Moreover this system can also be used to alert a remote system in a network. With the help of this system, we can use the camera in a restricted area and make the alarm to be raised in some other such as police station. In addition the system stores the images of the intrusion. We can also identify the thief using the stored picture .These features will make it distinguishable from other security systems by improving the performance of the system.