LDAP Error Code 49 : 80090308: LdapErr: DSID-0C090334, comm
LDAP: error code 49 shows in server.log.
ERROR: “auth.BaseLoginModule Failed login for <username>: [LDAP: error code 49 – 80090308: LdapErr: DSID-0C090334, comment: AcceptSecurityContext error, data 532, vece ]”
ERROR “2019-08-29 15:46:47.335 GMT-0500” 10.4.145.240 LDAPSync 0 0 18478 “actor=LDAPSyncService,text=[LDAPStore:getConnection] Could not bind to the directory server.VsException [error=18478] [javax.naming.AuthenticationException: [LDAP: error code 49 – 8009030C: LdapErr: DSID-0C09042A\, comment: AcceptSecurityContext error\, data 532\, v3839 ]],op=Synchronization”
https //www.voot.com/activate code and Login Account: Voot.com
Cause
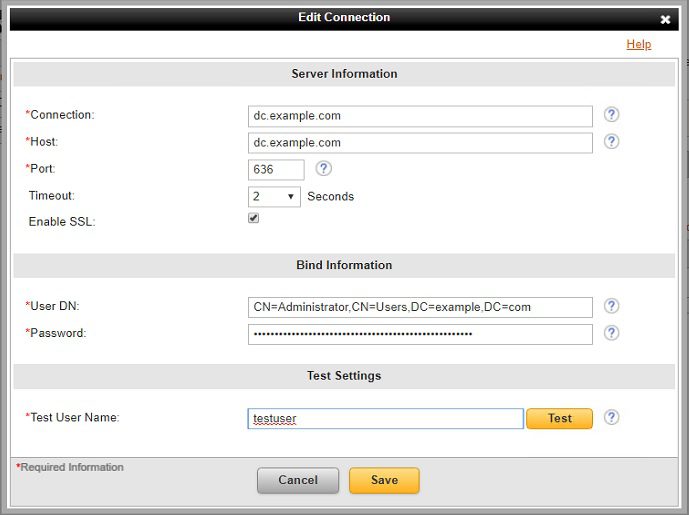
LDAP Error 49 implies an authentication failure when the VIP Enterprise Gateway (EGW) attempts to bind to the LDAP host specified in the EGW user store settings. Typically, the Distinguished Name (DN) or the password is invalid.
LDAP bind errors are returned by the LDAP connection IP address and captured in the VIP validation server logs. In the following example, error 49 and the specific sub-code (in hex) can be seen as returned from 10.4.5.240:
ERROR “2019-08-29 15:46:47.335 GMT-0500” 10.4.5.240 LDAPSync 0 0 18478 “actor=LDAPSyncService,text=[LDAPStore:getConnection] Could not bind to the directory server.VsException [error=18478] [javax.naming.AuthenticationException: [LDAP: error code 49 – 8009030C: LdapErr: DSID-0C09042A\, comment: AcceptSecurityContext error\, data 532\, v3839 ]],op=Synchronization”
com.apple.mobilephone Error 1035 : How to Fix the Error 1035?
LDAP Result Code 49 sub-codes for Authentication
ailures (source:https://ldapwiki.com/wiki/Common%20Active%20Directory%20Bind%20Errors):
525 user object not found
52e invalid password/credential
53f credential policy violation
530 time restriction in place
531 not permitted to logon at this workstation
532 password expired / DN username mismatch
533 account disabled
568 too many context identifiers
701 account expired
773 username/password valid, must reset password
775 account lockout
Resolution
Sub-error 532 can also be returned if the DN does not match the AD username.
To resolve, change the field User Distinguished Name (DN) on the User Stores page to use the full name from Active Directory and not the VIP user login name:
From Active Directory, navigate to the Users folder (or another folder where users with access to the Symantec Schema updates are configured)
https //m.facebook.com/watch/ Videos, Music and More on Facebook Mobile
Select is folder in the navigation pane. In the details pane, the name that is showing in the Name column field is the FullName.
If necessary, right-click it and choose Rename and rename it accordingly.
After renaming the user, a window will display the new name in the FullName field.
Note: This is the FullName used to perform the LDAP queries in Active Directory from VIP. As noted above, this error can also occur for other reasons.
Be the first to comment