





Published on Jan 09, 2026
THE success of future wireless systems will depend on the concepts and technology innovations in architecture and in efficient utilization of spectral resources. There will be a substantial need for more bandwidth as wireless applications become more and more sophisticated.
This need will not be satisfied by the existing frequency bands being allocated for public mobile radio even with very evolved and efficient transmission techniques.
Also wide ranges of potential spectral resources are used only very rarely. In the presented approach that is called spectrum pooling, different spectrum owners (e.g. military, trunked radio etc.) bring their frequency bands into a common pool from which rental users may rent spectrum. Spectrum pooling reflects the need for a completely new way of radio resource management. Interesting aspects of the spectral efficiency gain that is obtained with the deployment of spectrum pooling.
A potential rental system needs to be highly flexible with respect to the spectral shape of the transmitted signal. Spectral ranges that are accessed by licensed users have to be spared from transmission power. OFDM modulation is a candidate for such a system as it is possible to leave a set of subcarriers unmodulated. Thus, providing a flexible spectral shape that fills the spectral gaps without interfering with the licensed users.
A schematic example of this method is given in Fig. 1. Furthermore, spectrum pooling systems are not supposed to compete with existing and upcoming 2G and 3G standards. They are rather meant to be a complement in hot spot areas with a high demand for bandwidth (e.g.airports, convention centers etc.). Hence, it is straightforward to apply modified versions of OFDM based wireless LAN standards like IEEE802.11a and HIPERLAN/2.
There are many modifications to consider in order to make wireless LANs capable of spectrum pooling. They range from front end via baseband processing to higher layer issues. One important task when implementing spectrum pooling is the periodic detection of idle subbands of the licensed system delivering a binary allocation vector as shown in Fig. 1. A detailed description of how to perform this in an optimal fashion is given. We propose an approach where any associated mobile terminal of the rental system conducts its own detection.
This detection is the first step in a whole protocol sequence that is illustrated in Fig. 2. Having finished the detection cycle, the results are then gathered at the access point as visualized in Fig. 2b). The received information can be processed by the access point which basically means that the individual binary (allocated/deallocated) detection results are logically combined by an OR operation.
Thereafter, a common pool allocation vector which is mandatory for every mobile terminal is broadcast in a last phase as shown in Fig. (2c). It is shown that this distributed technique is more reliable and yields a higher system throughput than only having the access point conduct a spectral detection. However, if the collection of the detection results is realized by sending a MAC layer data packet for each mobile terminal, the signaling overhead will be very high as the number of mobile terminals can be as high as 250 in the considered wireless LAN systems.
Now, one could reduce the number of detecting mobile terminals. Unfortunately, this approach has several drawbacks.
The random choice of the detecting rental users would not guarantee an optimal spatial distribution of the detecting mobile terminals. The transmission of these results would still take a lot of time and their correct reception is disturbed by rental users that have accessed their subbands since the last detection cycle. One further problem is the redundancy in the measurement data. Several mobile terminals can encounter the same constellation of licensed user accesses. We investigated techniques like the adaptive tree walk protocol to reduce the amount of measurement data packets but none of them was satisfactory with respect to duration and robustness.
The basic idea behind the first phase is quite simple. Having performed their detection, the mobile terminals compare their detection result with the mandatory allocation vector that was broadcast by the access point after the last detection cycle. If a mobile terminal encounters a spectral access by a licensed user to a certain subband which was not announced by the access point, then it transmits complex symbols at maximum power level (e.g. 1 + j1) on these OFDM carriers where the new licensed user accesses were detected. This results in a power amplification of the licensed user signal. The remaining OFDM carriers are spared from energy by transmitting complex zeros (0 + j0).
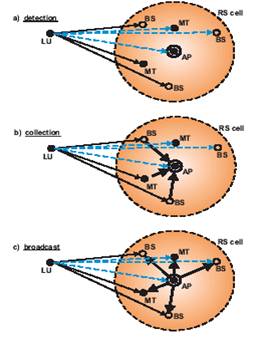
Fig.2 Protocol cycle of detection, collection and broadcast
The access point continues to detect the incoming signal which is a superposition of the transmitting licensed users and all the boosting signals of the mobile terminals. Thus, the licensed user signal has a boosted power level resulting in a higher detection probability at the access point. This boosting period TB1 has to be long enough in order to obtain the desired level of detection reliability. However, it is to be kept as short as possible as the boosting of the mobile terminals decreases the SNR of the licensed system. This trade-off is subject to further investigations.
This approach kills two birds with one stone. First, the detection results of all mobile terminals are gathered simultaneously. Hence, the transmission of an individual data frame containing the detection results for each mobile terminal is not necessary. This results in a substantial decrease of signaling overhead. Secondly, the additive superposition of the boosting signals replaces the necessary logical OR operation of the individual detection results at the access point and makes buffer memories dispensable.
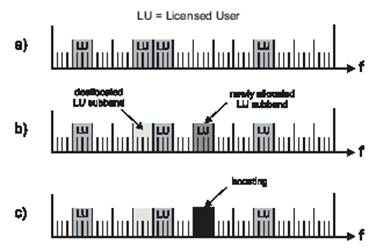
Fig. 3a depicts an exemplary common pool allocation which has been broadcast by the access point after the last detection cycle. After a new detection, an individual mobile terminal may encounter a new individual pool allocation as shown in Fig. 3b. One subband was newly allocated by a licensed user (dark gray). Another one was deallocated (light gray). The rest of the pool allocation remains unchanged. As described above, the OFDM carriers representing the newly allocated subband are boosted (Fig. 3c). This results in a much higher detection probability at the access point. Quantitative analytical and simulative evaluations of the relation between the received signal power and the detection probability.
| Are you interested in this topic.Then mail to us immediately to get the full report.
email :- contactv2@gmail.com |