





Published on Jan 09, 2026
Bitcoin became a fixture in world financial news in late 2013 and early 2014. The “virtual currency” had been launched five years earlier by computer hobbyists, and in late 2013 the U.S. dollar exchange rate for one bitcoin rose more than fivefold in the space of a few weeks. The market value of one bitcoin, which had begun trading at less than five cents in 2010, briefly exceeded $1,200.00.
Two days of hearings were held by the U.S. Senate Committee on Homeland Security and Governmental Affairs, and government regulators testified that algorithmic, stateless currencies like bitcoin had the potential to play useful roles in the commercial payment system.1 Stories appeared in the media about travelers subsisting for lengthy periods by spending only bitcoin, and various businesses, some of them exotic such as Richard Branson’s Virgin Galactic space travel, attracted publicity by accepting bitcoin as payment. The euphoric news surrounding bitcoin at the end of 2013 gave way to catastrophe in February 2014, when the Mt. Gox exchange, once the leader in worldwide bitcoin trading, imploded in a spectacular bankruptcy.
Hundreds of millions of dollars worth of bitcoins went missing in connection with the failure of Mt. Gox, yet the value of bitcoins on other exchanges remained surprisingly high at around $450 each at the time of this writing. Figure 1 shows the daily closing dollar-bitcoin exchange rate on the Mt. Gox exchange up until February 2014, and thereafter on the Bitstamp exchange, which took over the top spot in trading volume after Mt. Gox folded.
This section presents analyses of ways in which bitcoin fails to conform to the classical properties of a currency. A successful currency typically functions as a medium of exchange, a unit of account, and a store of value. Bitcoin faces challenges in meeting all three of these criteria.
Because bitcoin has no intrinsic value, its worth ultimately hinges upon its usefulness as a currency in the consumer economy. Evidence of bitcoin’s footprint in daily commerce is mostly anecdotal, consisting of newspaper stories about people living only by spending bitcoin or estimates of large numbers of businesses that are willing to accept bitcoin. To date, only one established business of any size has begun to take bitcoin, the online retailer Overstock.com. Most of the rankings of the top merchants accepting bitcoins are dominated by computer software and hardware companies selling products narrowly focused on bitcoin applications, and by marketplaces or exchanges providing investor services to bitcoin speculators.
Realistic insight into the adoption of bitcoin can be obtained from data drawn from the universal ledger of bitcoin transactions. According to data available at numerous websites, the recent bitcoin transaction count has peaked at daily volumes of approximately 70,000. However, it is widely understood that most of these transactions involve transfers between speculative investors, and only a minority are used for purchases of goods and services.
For instance, Fred Ersham, co-founder of Coinbase, the leading digital wallet service, estimated in a March 2014 interview that 80% of activity on his site was related to speculation, down from perhaps 95% a year earlier (Goldman Sachs, 2014). If we take this estimate as correct, then perhaps 15,000 bitcoin transactions per day involve the purchase of a product or service from a merchant. In a world with 7,000,000,000 consumers, most of whom make multiple economic transactions each day, bitcoin appears to have a extraordinarily negligible market presence.
For a currency to function as a unit of account, consumers must treat it as a numeraire when comparing the prices of alternative retail goods. For instance, a cup of coffee that costs $4.00 in one café is quickly understood to be twice as expensive as a cup of coffee selling for $2.00 at another café down the street. Bitcoin faces a number of obstacles in becoming a useful unit of account. One problem arises from its extreme volatility, an issue discussed in further detail below. Because the value of a bitcoin compared to other currencies changes greatly on a day-to-day basis, retailers that accept the currency have to recalculate prices very frequently, a practice that would be costly to the merchant and confusing to the consumer. In principle this issue would recede in an economy that used bitcoin as its principal currency, but no such place exists in today’s world.
A related problem stems from the diversity of “current market prices” that one can obtain for bitcoin at any given time. For instance, at the moment of writing this paragraph, I consulted a widely used website that posts the prices of bitcoins on markets around the world. The five exchanges with the highest trading volume quoted U.S. dollar prices for one bitcoin of $454.81, $453.60, $462.12, $450.84, and $480.15, all for trades having taken place within the several minutes. This disparity of market values, ranging by almost 7% between the high and low quotes, is a clear violation of the classical law of one price, and it would be unthinkable for these conditions to persist in a developed currency market due to the ease of arbitrage.
The uncertain market value of one bitcoin presents a conundrum for any third party vendor or customer seeking to establish a valid reference point for setting consumer prices. As a result, many websites have taken to relying upon unwieldy price aggregations, such as the average bitcoin price over several exchanges over the past 24 hours, but these aggregates do not indicate to merchants and consumers the true cost of procuring or selling a bitcoin at the present time.
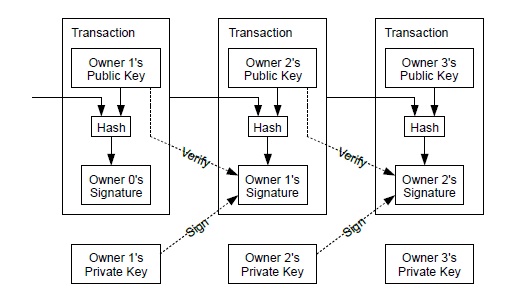
We define an electronic coin as a chain of digital signatures. Each owner transfers the coin to the next by digitally signing a hash of the previous transaction and the public key of the next owner and adding these to the end of the coin. A payee can verify the signatures to verify the chain of ownership.
The problem of course is the payee can't verify that one of the owners did not double-spend the coin. A common solution is to introduce a trusted central authority, or mint, that checks every transaction for double spending. After each transaction, the coin must be returned to the mint to issue a new coin, and only coins issued directly from the mint are trusted not to be double-spent. The problem with this solution is that the fate of the entire money system depends on the company running the mint, with every transaction having to go through them, just like a bank.
We need a way for the payee to know that the previous owners did not sign any earlier transactions. For our purposes, the earliest transaction is the one that counts, so we don't care about later attempts to double-spend. The only way to confirm the absence of a transaction is to be aware of all transactions. In the mint based model, the mint was aware of all transactions and decided which arrived first. To accomplish this without a trusted party, transactions must be publicly announced [1], and we need a system for participants to agree on a single history of the order in which they were received. The payee needs proof that at the time of each transaction, the majority of nodes agreed it was the first received.
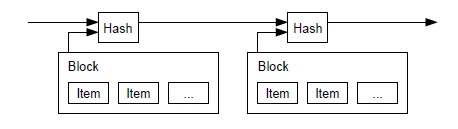
The solution we propose begins with a timestamp server. A timestamp server works by taking a hash of a block of items to be timestamped and widely publishing the hash, such as in a newspaper or Usenet post [2-5]. The timestamp proves that the data must have existed at the time, obviously, in order to get into the hash. Each timestamp includes the previous timestamp in its hash, forming a chain, with each additional timestamp reinforcing the ones before it.
To implement a distributed timestamp server on a peer-to-peer basis, we will need to use a proofof- work system similar to Adam Back's Hashcash [6], rather than newspaper or Usenet posts. The proof-of-work involves scanning for a value that when hashed, such as with SHA-256, the hash begins with a number of zero bits. The average work required is exponential in the number of zero bits required and can be verified by executing a single hash. For our timestamp network, we implement the proof-of-work by incrementing a nonce in the block until a value is found that gives the block's hash the required zero bits. Once the CPU effort has been expended to make it satisfy the proof-of-work, the block cannot be changed without redoing the work. As later blocks are chained after it, the work to change the block would include redoing all the blocks after it.
The proof-of-work also solves the problem of determining representation in majority decision making. If the majority were based on one-IP-address-one-vote, it could be subverted by anyone able to allocate many IPs. Proof-of-work is essentially one-CPU-one-vote. The majority decision is represented by the longest chain, which has the greatest proof-of-work effort invested in it. If a majority of CPU power is controlled by honest nodes, the honest chain will grow the fastest and outpace any competing chains. To modify a past block, an attacker would have to redo the proof-of-work of the block and all blocks after it and then catch up with and surpass the work of the honest nodes. We will show later that the probability of a slower attacker catching up diminishes exponentially as subsequent blocks are added. To compensate for increasing hardware speed and varying interest in running nodes over time, the proof-of-work difficulty is determined by a moving average targeting an average number of blocks per hour. If they're generated too fast, the difficulty increases.
The steps to run the network are as follows:
1) New transactions are broadcast to all nodes.
2) Each node collects new transactions into a block.
3) Each node works on finding a difficult proof-of-work for its block.
4) When a node finds a proof-of-work, it broadcasts the block to all nodes.
5) Nodes accept the block only if all transactions in it are valid and not already spent.
6) Nodes express their acceptance of the block by working on creating the next block in the chain, using the hash of the accepted block as the previous hash.
Nodes always consider the longest chain to be the correct one and will keep working on extending it. If two nodes broadcast different versions of the next block simultaneously, some nodes may receive one or the other first. In that case, they work on the first one they received, but save the other branch in case it becomes longer. The tie will be broken when the next proofof- work is found and one branch becomes longer; the nodes that were working on the other branch will then switch to the longer one.
New transaction broadcasts do not necessarily need to reach all nodes. As long as they reach many nodes, they will get into a block before long. Block broadcasts are also tolerant of dropped messages. If a node does not receive a block, it will request it when it receives the next block and realizes it missed one.
By convention, the first transaction in a block is a special transaction that starts a new coin owned by the creator of the block. This adds an incentive for nodes to support the network, and provides a way to initially distribute coins into circulation, since there is no central authority to issue them. The steady addition of a constant of amount of new coins is analogous to gold miners expending resources to add gold to circulation. In our case, it is CPU time and electricity that is expended. The incentive can also be funded with transaction fees.
If the output value of a transaction is less than its input value, the difference is a transaction fee that is added to the incentive value of the block containing the transaction. Once a predetermined number of coins have entered circulation, the incentive can transition entirely to transaction fees and be completely inflation free.The incentive may help encourage nodes to stay honest. If a greedy attacker is able to assemble more CPU power than all the honest nodes, he would have to choose between using it to defraud people by stealing back his payments, or using it to generate new coins.
He ought to find it more profitable to play by the rules, such rules that favour him with more new coins than everyone else combined, than to undermine the system and the validity of his own wealth.
Once the latest transaction in a coin is buried under enough blocks, the spent transactions before it can be discarded to save disk space. To facilitate this without breaking the block's hash, transactions are hashed in a Merkle Tree, with only the root included in the block's hash. Old blocks can then be compacted by stubbing off branches of the tree. The interior hashes do not need to be stored.
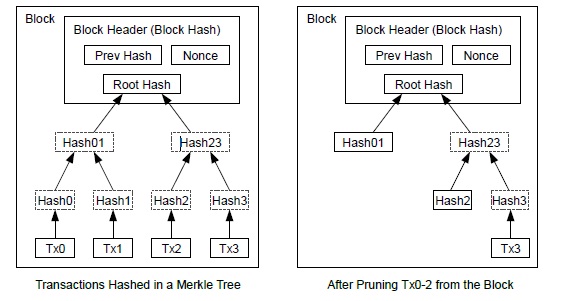
A block header with no transactions would be about 80 bytes. If we suppose blocks are generated every 10 minutes, 80 bytes * 6 * 24 * 365 = 4.2MB per year. With computer systems typically selling with 2GB of RAM as of 2008, and Moore's Law predicting current growth of 1.2GB per year, storage should not be a problem even if the block headers must be kept in memory.
The traditional banking model achieves a level of privacy by limiting access to information to the parties involved and the trusted third party. The necessity to announce all transactions publicly precludes this method, but privacy can still be maintained by breaking the flow of information in another place: by keeping public keys anonymous. The public can see that someone is sending an amount to someone else, but without information linking the transaction to anyone. This is similar to the level of information released by stock exchanges, where the time and size of individual trades, the "tape", is made public, but without telling who the parties were.
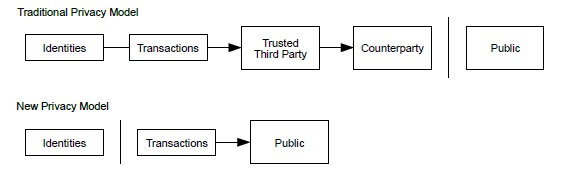
As an additional firewall, a new key pair should be used for each transaction to keep them from being linked to a common owner. Some linking is still unavoidable with multi-input transactions, which necessarily reveal that their inputs were owned by the same owner. The risk is that if the owner of a key is revealed, linking could reveal other transactions that belonged to the same owner.
We have proposed a system for electronic transactions without relying on trust. We started with the usual framework of coins made from digital signatures, which provides strong control of ownership, but is incomplete without a way to prevent double-spending. To solve this, we proposed a peer-to-peer network using proof-of-work to record a public history of transactions that quickly becomes computationally impractical for an attacker to change if honest nodes control a majority of CPU power. The network is robust in its unstructured simplicity. Nodes work all at once with little coordination.
They do not need to be identified, since messages are not routed to any particular place and only need to be delivered on a best effort basis. Nodes can leave and rejoin the network at will, accepting the proof-of-work chain as proof of what happened while they were gone. They vote with their CPU power, expressing their acceptance of valid blocks by working on extending them and rejecting invalid blocks by refusing to work on them. Any needed rules and incentives can be enforced with this consensus mechanism.
[1] W. Dai, "b-money," http://www.weidai.com/bmoney.txt, 1998.
[2] H. Massias, X.S. Avila, and J.-J. Quisquater, "Design of a secure timestamping service with minimal trust requirements," In 20th Symposium on Information Theory in the Benelux, May 1999.
[3] S. Haber, W.S. Stornetta, "How to time-stamp a digital document," In Journal of Cryptology, vol 3, no 2, pages 99-111, 1991.
[4] D. Bayer, S. Haber, W.S. Stornetta, "Improving the efficiency and reliability of digital time-stamping," In Sequences II: Methods in Communication, Security and Computer Science, pages 329-334, 1993.
[5] S. Haber, W.S. Stornetta, "Secure names for bit-strings," In Proceedings of the 4th ACM Conference on Computer and Communications Security, pages 28-35, April 1997.
| Are you interested in this topic.Then mail to us immediately to get the full report.
email :- contactv2@gmail.com |