



Published on Nov 30, 2023
Now-a-days it has become very easy for an adversary to steal the password hash file and crack the hash passwords. Thus, the threat for each user accounts continues to increase rapidly. As the cybersecurity threats are increasing, new mechanism needs to be developed. To detect the password file breach, Juels and Rivest had introduced the concept of decoy passwords known as “Honeywords”. For every user account, set of false passwords are generated using honeyword generation techniques. So, the hashed password databases consists of actual passwords and false passwords. For an adversary, when a password file is cracked, it becomes difficult to judge the real password. Honeyword model sets off an alarm if any of the honeyword is entered, notifying about the password file breach. Thus, there is a huge risk of an adversary being detected. In our model, we are implementing the decoy mechanism for protection of data from an unauthorized user and also tracking the IP of the detected user to take action against the malicious user.
Keywords: — Blocking, Decoy, Honeywords, IP, Intruder.
Face recognition focuses on still images, which can be broadly grouped into image-based and feature-based approaches. Face recognition is commonly used in applications such as human-machine interfaces, automatic access control systems and forensic investigations etc. which involves comparing a face image with a database of stored faces in order to identify the face in the image. This project involves the design and development of a forensic face sketch identification system. The 2D-DCT image compression technique is used to compress the cropped facial features of the image database like frontal face, left eye, right eye, nose and lips. After compression the image pixels reshaping is used for preparing the image classes as an input for the neural network. The SOM (Self Organizing Maps) neural network algorithm is designed for training of image data. The un-supervised weight is assigned during the training and learning in simulink for different number of epochs to classify and inputted face sketch. This project is based on general architecture of facial recognition systems. Program source code and simulation is executed in MATLAB and Simulink.
Prevention and Detection of an unauthorized access of the system is called as Computer Security. For securing the system is necessary to follow three steps.
Prevention – Stopping the action from happening or occurring is called as Prevention.
Detection – Noticing the presence of some failure is called as Detection.
Reaction – Responding to the failure is called as Reaction.
Everywhere the system has become an important element of day to day life. As all the relevant data is stored on the system, it necessary that system should be secure enough. The most widely used authentication method which proves better in standards such as usability and security is authentication based on Password. It is important that passwords must be protected and secure enough to avoid different attacks. Now-a-days many companies store their important data in databases [1]. It is very easy for an intruder to get the username and password by using emerging and new password cracking techniques. So for avoiding password related issues, Honeyword concept was introduced.
Honeywords are false or decoy passwords which are generated using different generating algorithms. It is a set of words which are some wat similar to the password submitted by the user for a particular account. For every user account the set of honeywords are generated. Honeywords are generated using generator algorithm. Honeywords concept was introduced to detect the failure and an unauthorized access. In our system, we are introducing the concept of IP Blocking as Reaction towards the detected intruders.
Decoy data mechanism is also called as Fog Computing. This concept is basically introduced for confusing the attacker and making difficult from him to distinguish between the sensitive data (worth data) from the irrelevant data (worthless data). It helps in securing the real data of the user from being misused. Fake (Decoy) files are made available only when unauthorized access is detected by the honeyword generation scheme.
IP address blocking is used for disabling the access of an unauthorized users. It is very important for introducing this concept in honeyword model for maintaining the security of the system. Blocked IP address can be added in blacklist for avoiding the misuse of the system and keeping it secure from various types of attacks.
Most businesses today know the need to have a strong data security strategy to protect themselves, their employees and their customers from various security threats. Generally many companies and software industries store their data in ORACLE or Mysql or may be other. So, for entry into the system which is required is user name and password. Once a password file is sacked, by the password cracking technique it is easy to get most of the passwords. In previous years many companies like LinkedIn, Yahoo, and eHarmony were affected due to password leaks because of following weak security practices. To increase the security the honeywords concept was introduced. In honeyword system it is sure that the attacker will be detected. But due to some reason, till now no action was taken against the unauthorized access detected. The proposed system tries to fill this void by proposing a new technique where we detect the unauthorized user and block him with the help of his IP address and we also protect the sensitive and relevant data of the user by providing the fake worthless data to the adversary.
We use honeywords mechanism to launch disinformation attacks against unauthorized insiders, preventing them from distinguishing the original sensitive customer data from fake worthless data. In this work we will use an already wellestablished method of honeyword generation and have used a logic of ASCII to generate honeywords and SHA-256 algorithm for hashing. The attempted use of a honeyword for login will set off an alarmto the administrator and user about the password file breach. After more than 3 incorrect attempts the unauthorized user will be given access to decoy files. System will also keep track of IP.Using IP tracking we can avoid unwanted request from a single system thus reducing the unnecessary computation
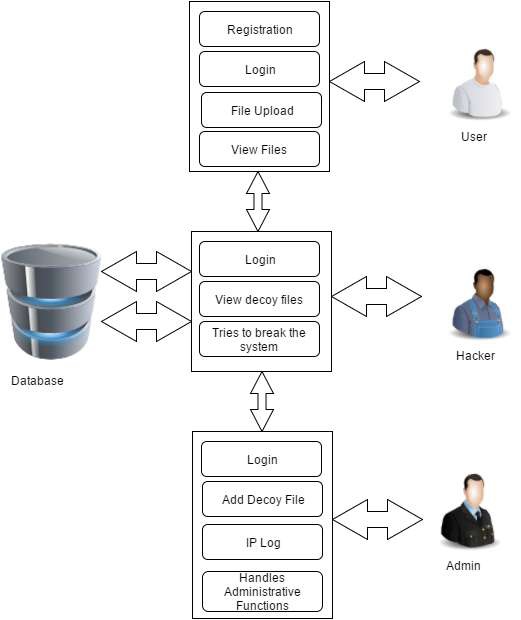
A person who has an authorized access to the system is said to be a user. Here, User is going to register into system. While registration, for the given password by the user the system generates honeywords using honeyword generation technique. User login into the system using his unique email id and password. If password matches with the hash of the original password then user gets access to the system. For a valid login, the access to his actual data will be given. Hacker tries to login into the system. If he enters any honeyword then the alert is given to the Actual user and the admin through an email. And if suppose he try combination of password or any honeyword and it goes more than three attempt then he get access but to the decoy files. Decoy files are fake files which are displayed to the intruder when a failure or an unauthorized access is detected. For every login, whether the attempt is valid or invalid the IP is tracked. Log of number of attempts is also maintained in the database for every user id which will be help us to take necessary action.
The main aim of project is validating whether data access is authorized or not when abnormal information access is detected and taking appropriate action against unauthorized access detection. Basically, confusing the attacker with fake information. This protects against the exploitation of the user’s real data. We propose a completely different approach for securing the data using decoy information mechanism. We use this honeyword technology to launch deceptive attacks against wicked insiders, preventing them from distinguishing the actual real customer data from fake irrelevant data. The addition of IP tracking module in this proposed model helps to block the unauthorized access thus providing the better system security.
[1] M. Dennis and Justin Cappos, "Understanding password database compromises," Dept. of Computer Science and Engineering Polytechnic Inst. of NYU, 2013.
[2] Brown and Kelly, "The dangers of weak hashes," SANS Institute Infosec Reading Room, November 2013.
[3] I. Erguler, "Achieving Flatness: Selecting the Honeywords from Existing User Passwords," IEEE Transactions on Dependable and Secure Computing, IEEE, vol. 13, no. 2, p. 284 – 295, February 2015.
[4] A. Juels and R. L. Rivest, "Honeywords: Making Password cracking Detectable," In Proceedings of the 2013 ACM SIGSAC conference on Computer & communications security, p. 145–160, November 2013.